Carding Tutorial
If you want to start carding. Just read our all of carding tutorial. Our tutorial help you start your carding journey.

Carding Tutorial: How to Buy Real Credit Card Numbers Safely and Securely
In today's digital world, "carding" is a big worry. Cybercriminals are after personal and financial info. Carding means using credit or debit cards without permission. It's illegal and hurts many people. This article warns against it and explains the dangers.........
Read More
From Dumps with Pins to Valid Credit Card Numbers: Exploring the Dark Web's Carding Underworld
Welcome to the world of carding. It's all about illegally using or selling credit cards. This shadow economy started small but is now big and complex. It involves many ways to get your financial details and use them to make.........
Read More
Uncovering the World of CVV Shops and Dump Stores: What You Need to Know
Credit and debit cards are now a popular way to pay for things. But, there's a big problem with fraud. It's making people worry about their privacy and if they can trust their cards. Some big names like Capital One,.........
Read More
Don't Risk It! Top Mistakes to Avoid When Buying CC Dumps
The world of credit card fraud is a dangerous place. There's an underground market for compromised credit card data. This data is called "CC dumps" and is a big risk for everyone. This article will give you tips to stay.........
Read More
The Ultimate Guide to Carding Methods and Cashing Cards: How to Stay Safe Online
In today's digital world, credit card fraud, or "carding," is a big issue for everyone. It involves using stolen credit or debit card details for wrongdoing. This isn't just dangerous for your money. It can also harm the wider economy.
The.........
Read More
"Master Carding Methods: Cashing Cards, CVV Carding & More | Carding Tutorial | carding methods
​In the deep web, where anonymity reigns, a highly lucrative and illegal practice called "carding" is thriving. Carding involves unauthorized access to credit card numbers and using them for fraudulent activities. There are various methods used in the dark underbelly.........
Read More
The Ultimate Guide to Cashing Card and CVV Shop High Balance | cc carding | valid cc shop | cvvshop
Are you looking to take your credit card fraud game to the next level? Look no further than our Ultimate Guide to Cashing Card and CVV Shop High Balance! In this comprehensive blog post, we will walk you through all.........
Read More
The Best Online CC Shop – Find Your Perfect Credit Card
If you're looking for an online CC shop, here are a few of the best options:
Venturing into the expansive realm of credit cards unveils a myriad of possibilities. The labyrinth of choices encompasses online shopping, in-store indulgences, and the mundane.........
Read More
Safely Buy CC, Dumps, and Fullz for Carding With Cashing Card
In the annals of contemporary cyberspace, the specter of cybercrime looms ever larger, casting a sinister shadow across the digital realm. It is within this murky underbelly that we find the insidious rise of illicit endeavors, a burgeoning underworld where.........
Read More
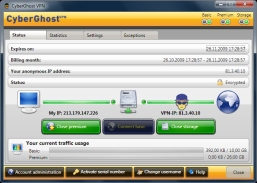
cc shop online • cvv shop high balance, With Stop Wasting Money on Anti-Virus Software when You can get it Free
Its no secret that there are many dangers lurking on the Internet.

There are viruses, worms, trojan horses and malicious programs waiting to infect your computer each and every day. And though there are countless.........
Read More
Hack Facebook Password, With fullz shop | cvv fullz | cc fullz | cvv dumps | cvv sites.
Wondering to know how to hack Facebook password? Well, before you can do that, it is very much necessary to understand the real ways of hacking that actually work and also those that are simply scam and do not work. So in.........
Read More
Trusted cvv shop 2023 | dumps with pin | valid cc shop | best dumps website 2023, With - What is carding?
What is carding?
Carding refers to the process of using stolen credit card information to make fraudulent purchases online or in-person. This illegal activity has been around for decades and has become increasingly sophisticated in recent years with the rise of.........
Read More
Validcc | ccshop | cvvshop | cc fullz | cc dumps, With Password Hacking FAQ
Some of the password basics
Most accounts on a computer system usually have some method of restricting access to that account, usually in the form of a password. When accessing the system, the user has to present a valid ID to.........
Read More
Trusted cc shop • validcc • ccshop • cvvshop - With How to Surf Anonymously for Free without the use of a Proxy.
When creating a connection you are given a unique IP address from your provider that clearly identifies you for the duration of the session (and for a long while after).
Once online, your movements leave behind.........
Read More
Best cvv shop 2023 • dumps carding • card dumps - With Top 5 Hacking and Security tools.
Top 5 Hacking and Security Tools.
Today we present the top 5 best hacking/security tools which are highly usable in securing and exploiting your computer or network. These tools are designed in a way that they can collect information required to.........
Read More
How To Hack Wi-Fi Of Your Neighbor - With trusted cvv shop 2023 • dumps with pin • valid cc shop.
How To Hack Wi-Fi Of Your Neighbor:

You surely love using high speed internet. And if it comes to you at no cost then its like paradise on earth. Suppose you have a nice, loving neighbor.........
Read More
Buying a Valid CC with High Balance | best cvv shop 2023 - With Smartphone 7 Apps Tha Secretly Compose As Remote Controls.
Buying a Valid CC with High Balance | best cvv shop 2023.
In today's digital world, online shopping has become the norm. With more and more people opting to make purchases online, the need for a valid credit card has become.........
Read More
How to Find a Valid Best CC Shop - With Tips for you Knowing About Settings and Tricks of Window Phones.
How to Find a Valid Best CC Shop:-
In today's digital world, online shopping has become the norm. With more and more people opting to make purchases online, the need for a valid credit card has become essential. However, with credit.........
Read More
Top 10 ways to protect your ATM / Debit / Credit card from Hackers | how to protect ATM Hacking. With cc shop online | dumps and pins | fresh cvv shop
In today’s article, we will look at the activities of ATM card skimmers or the black-hat hackers on ATM PIN number and how to protect your PIN number from these sharp practices. In my last post, I pointed it out that.........
Read More
Hack A Facebook Password ~ Best Hacking Ways - With cvv sites • validcvv • valid dumps • dump shop
Hello Friends, We’ll today discuss the most fascinating question among youth i.e How to hack a Facebook Password.Facebook is the largest social network with over 600 million users in the world. As a consequence, more and more people ask for.........
Read More
cvv dumps • dumps with pin • valid dumps • cc dumps With Facebook timeline latest review ~ Facebook Timeline
Facebook timeline latest review ~ Facebook Timeline
I’ve often joked that if something’s not on Facebook, it didn’t happen. Facebook’s new Timeline feature makes that adage even more apparent.
Timeline is Facebook’s new way of presenting you to the world. It replaces your traditional.........
Read More