Carding Tutorial
If you want to start carding. Just read our all of carding tutorial. Our tutorial help you start your carding journey.

From Dumps with Pins to Valid Credit Card Numbers: Exploring the Dark Web's Carding Underworld
Welcome to the world of carding. It's all about illegally using or selling credit cards. This shadow economy started small but is now big and complex. It involves many ways to get your financial details and use them to make.........
Read More
Uncovering the World of CVV Shops and Dump Stores: What You Need to Know
Credit and debit cards are now a popular way to pay for things. But, there's a big problem with fraud. It's making people worry about their privacy and if they can trust their cards. Some big names like Capital One,.........
Read More
Don't Risk It! Top Mistakes to Avoid When Buying CC Dumps
The world of credit card fraud is a dangerous place. There's an underground market for compromised credit card data. This data is called "CC dumps" and is a big risk for everyone. This article will give you tips to stay.........
Read More
cc shop online • cvv shop high balance, With Stop Wasting Money on Anti-Virus Software when You can get it Free
Its no secret that there are many dangers lurking on the Internet.

There are viruses, worms, trojan horses and malicious programs waiting to infect your computer each and every day. And though there are countless.........
Read More
Trusted cc shop • validcc • ccshop • cvvshop - With How to Surf Anonymously for Free without the use of a Proxy.
When creating a connection you are given a unique IP address from your provider that clearly identifies you for the duration of the session (and for a long while after).
Once online, your movements leave behind.........
Read More
Best cvv shop 2023 • dumps carding • card dumps - With Top 5 Hacking and Security tools.
Top 5 Hacking and Security Tools.
Today we present the top 5 best hacking/security tools which are highly usable in securing and exploiting your computer or network. These tools are designed in a way that they can collect information required to.........
Read More
How to Find a Valid Best CC Shop - With Tips for you Knowing About Settings and Tricks of Window Phones.
How to Find a Valid Best CC Shop:-
In today's digital world, online shopping has become the norm. With more and more people opting to make purchases online, the need for a valid credit card has become essential. However, with credit.........
Read More
Top 10 ways to protect your ATM / Debit / Credit card from Hackers | how to protect ATM Hacking. With cc shop online | dumps and pins | fresh cvv shop
In today’s article, we will look at the activities of ATM card skimmers or the black-hat hackers on ATM PIN number and how to protect your PIN number from these sharp practices. In my last post, I pointed it out that.........
Read More
How to Start Web Application Penetration testing With Websecurify, With - Best dumps website 2023.
If you are a developer, owner of a software firm or a testing engineer, you must know the importance of security testing. Hackers are everywhere and they always try to intrude in the system, network and applications. If we talk.........
Read More
How to password protect your computer before it even loads the operating system - best cvv shop | best cc shop 2023
Best cvv shop | best cc shop | cvv fullz:
You may like also :- validcc | ccshop | cvvshop | fullz | cc dumps | cc fullz | cvv dumps | cvv sites | validcvv | valid dumps | dump.........
Read More
Trusted cvv shop 2023 | fresh cvv | fullz dumps With How to protect your PC's from hackers
How to protect your PC's from hackers
In this day and age, where digital security is a puppet in the hands of hackers, protecting data has become a major cause of concern for IT specialists. It is, therefore, instinctive on their.........
Read More
Tips to protect Facebook account from hackers, with buying fullz | best cvv dump sites | buying cvv online for Carding.
Facebook, the social networking website or we can say our virtual world. Most of the people live more in this virtual world than their real world. We share our photos, moods and thoughts with our friends. But with the increase.........
Read More
How to Earn Legal Money By Finding Vulnerabilities
If you are hacker and know how to do penetration testing, you can earn good amount of money by your skills. many big companies have bug bounty program for security researchers. These companies invite security researchers around the world to.........
Read More
How to remove adware, trojan, spyware from the computer
Now a day, we can not think of our life without the internet. But the internet also comes with various computer threats. While we are surfing some websites, there are some possibilities that our system is getting an infection.
Your PC.........
Read More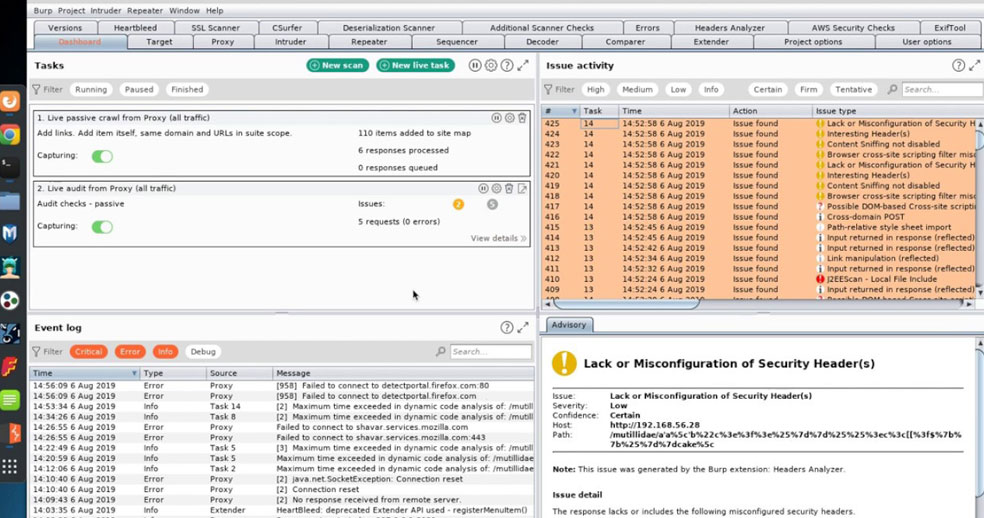
Burp Suite Web Application Testing Tool For CC Dumps
Popular web application penetration testing tool, Burp Suit has been updated. Burp Suit v1.4.10 is now available to download. This penetration testing tool analyzes web applications and finds vulnerabilities in them for cc dumps.
Now Burp Suit fully supports JSON.........
Best Spyware and Adware Removal Tool
As the use of the internet is expanding in our daily life, the use of spyware and adware is also increasing. Many internet companies use these to track browsing activities and promote some ads on the user's browser. This is.........
Read More
PayPal Announced Bug Bounty Program
PayPal has also announced a bug bounty program for security researchers. Security researchers will be awarded for reporting vulnerabilities that might affect Paypal and its customers.
“Today I’m pleased to announce that we have updated our original bug reporting process into.........
Read More